Linux kernel security is under fire. On Wednesday, a vulnerability dubbed ‘Copy Fail’ (CVE-2026-31431) was disclosed, and the clock is ticking for distributions worldwide to get patches into users’ hands. This isn’t just theoretical; a proof-of-concept exploiting the flaw with just a few hundred bytes of data was released simultaneously with the disclosure, meaning the exploit is already loose in the wild.
The Immediate Threat: Privilege Escalation via Code
Here’s the stark reality: ‘Copy Fail’ is a local privilege escalation vulnerability. In plain English, it means an attacker who already has minimal access to a Linux system can use this flaw to become a superuser, gaining administrative control. The fact that the proof-of-concept requires such a tiny amount of code is alarming. It’s the digital equivalent of a locksmith being handed a skeleton key that opens nearly every door, and that key is now in circulation.
While Theori, the security firm that discovered the exploit, did provide a five-week heads-up to the Linux kernel security team, that window was primarily for patch development. The public release of the exploit means that while many kernel versions have patches ready, the integration into specific distributions is the real bottleneck.
“This PoC was released into the wild on Wednesday when the vulnerability was disclosed, which means that by now it’s in the hands of every bad guy on the planet who wants it.”
This is the core of the problem. The kernel may be fixed, but have your distribution’s maintainers incorporated that fix into their packages and pushed it out through their update channels? For many, the answer is still a work in progress.
Distribution Patching: A Scramble to Secure Systems
The market dynamics here are clear: a critical zero-day-adjacent vulnerability hitting a dominant open-source operating system. Every distribution, from the giants like Ubuntu and Red Hat to smaller players, is now in a high-stakes race. Some, like Arch Linux with its rolling release model, are likely to get the patches out faster, incorporating upstream fixes directly into their continually updated kernels. Others, especially those with more traditional release cycles or complex backporting processes, face a longer road.
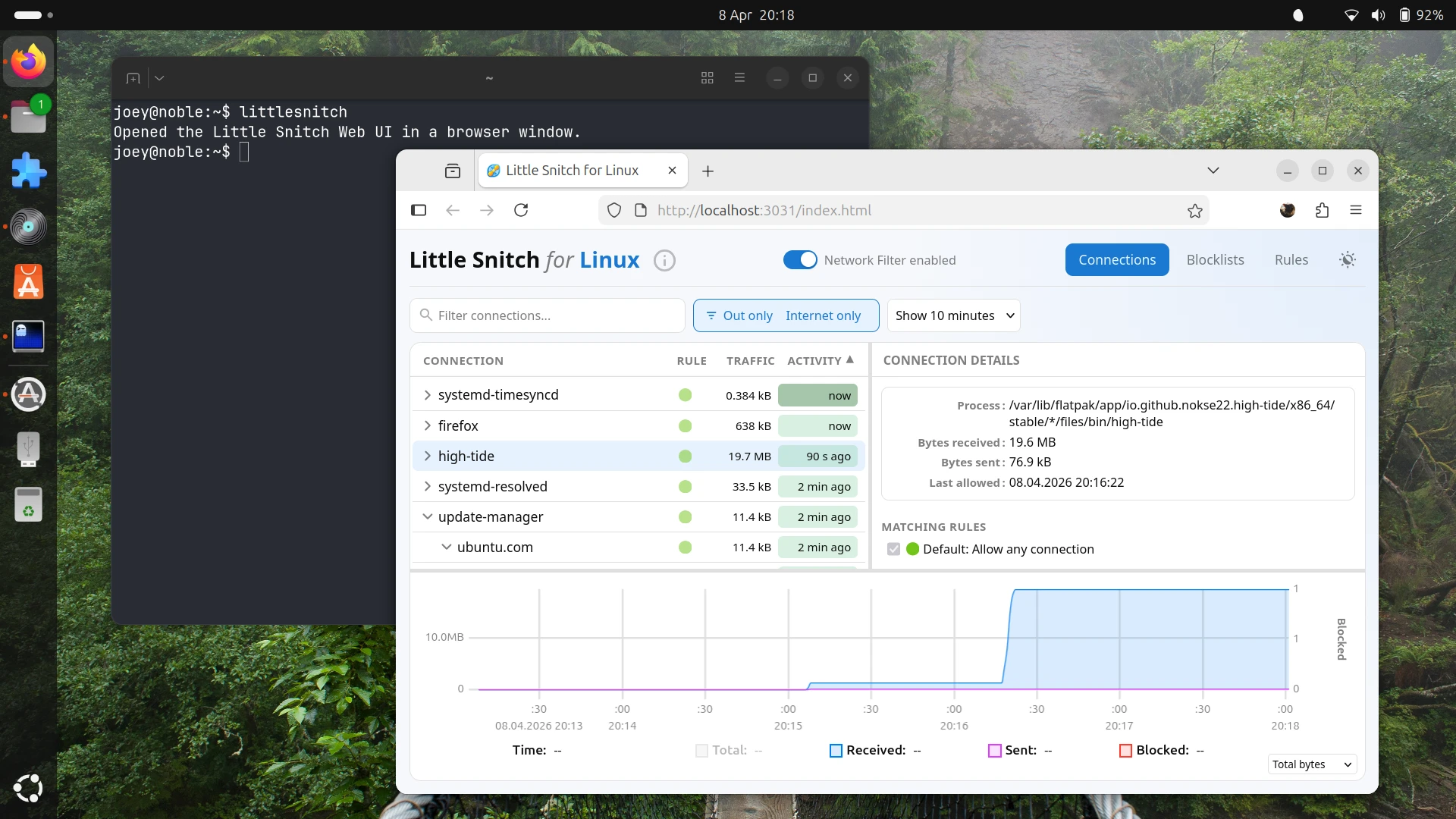
My own experience with Linux Mint highlighted the current friction. Update mirrors were sluggish, and attempts to refresh repository information timed out—a frustrating experience exacerbated by ongoing DDoS attacks against Ubuntu, Mint’s upstream. This illustrates the cascading effects of system-level issues; a patch might be ready, but getting it to you can be anything but smooth.
Here’s a look at the status across major distros, though this is a rapidly evolving situation:
| Distro/family | Copy Fail Patch Status (CVE-2026-31431) |
|---|---|
| Linux mainline kernel | Fixed in 7.0 and later, 6.19.12, 6.18.22, 6.18.12, 6.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254 |
| Ubuntu | Fix via updated Ubuntu kernel packages |
| Debian | Fix via kernels listed in Debian security tracker |
| RHEL | Fix via Red Hat kernel errata (backported patch) |
| SUSE / openSUSE | Fix via SUSE kernel updates |
| Amazon Linux | Fix via updated Amazon Linux kernels |
| Arch Linux | Fix via rolling kernel including upstream patch |
| Fedora (42+) | Fix via updated Fedora kernels |
| Gentoo | Fix via updated kernel ebuilds |
| CloudLinux | Fix via CloudLinux kernels / KernelCare patches |
| AlmaLinux | Fix via AlmaLinux kernel updates |
| Linux Mint | Expected via Ubuntu kernel once Mint syncs |
This table is a snapshot. The critical takeaway for anyone running Linux, particularly those managing servers, is to actively monitor your distribution’s security advisories and update channels. The “door” for an attacker is likely local, meaning they need some initial access—perhaps through a phishing email, a vulnerable web service, or a compromised user account. For desktop users, this means exercising caution with downloads and links until your system is confirmed to be patched.
What Does This Mean for Open Source Development?
This incident, while concerning, underscores a fundamental strength of the open-source ecosystem: transparency and rapid community response. The vulnerability was found, privately reported, and patches were developed relatively quickly. The challenge isn’t the development of the fix; it’s the distribution and deployment of that fix across a fragmented landscape of user configurations.
It also highlights the perennial tension between security and usability. The delay between kernel patch availability and distro deployment is an inherent friction point. This isn’t a failing of Linux, but a reality of managing complex, open systems with diverse needs. For commercial vendors like Red Hat and SUSE, the ability to backport patches efficiently and communicate their availability is a key selling point.
For the average Linux user, the advice is straightforward but urgent: keep your systems updated. Pay attention to specific notifications about ‘Copy Fail’ or CVE-2026-31431. Once available, apply the updates immediately. Don’t wait.
This isn’t a moment for panic, but for diligent action. The open-source community has the tools to defend itself; now it’s about ensuring those tools are deployed effectively to every endpoint.
🧬 Related Insights
- Read more: Latin America’s Open Source AI Surge: Drones Deliver, Robots Rise, Co-Creation Beckons
- Read more: [Voice AI File Manager] Neat Hack, Real Mess?
Frequently Asked Questions
What is the ‘Copy Fail’ exploit?
‘Copy Fail’ (CVE-2026-31431) is a security vulnerability in the Linux kernel that allows an unprivileged user to escalate their privileges to administrative control. It can be exploited with a small amount of code.
How can I protect myself from the ‘Copy Fail’ exploit?
The primary protection is to update your Linux distribution’s kernel to a patched version as soon as it becomes available. Monitor your distro’s official security advisories and update manager closely.
Is my Linux system at immediate risk if it’s not updated?
If your system is not patched and an attacker gains even minimal local access, it is at risk. The exploit requires an initial foothold on the system, often gained through social engineering or other vulnerabilities.